First of all sorry to all my readers for posting so late...Now coming to the point I would like to tell you that bookmyshow has started a referral offer in which we will get 100 rs each ...many of you might be knowing it also but today I came to know that to reffer first you have to add some money from your credit card then you will get 100 rs or your refferal code ....don't worry I have added some money in my account and got my code....you all can use my code:-G429LCX and get 100 rs without adding any money and you will get a discount of 100rs on booking your tickets and after booking your tickets you will get your refferal code for free also ...so what are you waiting for just grab this offer before it expires... It's your choice😎.
Thursday, 24 December 2015
Sunday, 8 November 2015
Basics for Hacking
Hacker means someone who finds weaknesses in a computer or computer network, though the term can also refer to someone with an advanced understanding of computers and computer networks.Hackers may be motivated by a multitude of reasons, such as profit, protest, or challenge. The subculture that has evolved around hackers is often referred to as the computer underground but it is now an open community. While other uses of the word hacker exist that are not related to computer security, they are rarely used in mainstream context.
Classifications:-
Several subgroups of the computer underground with different attitudes use different terms to demarcate themselves from each other, or try to exclude some specific group with which they do not agree. Eric S. Raymond (author of The New Hacker's Dictionary) advocates that members of the computer underground should be called crackers. Yet, those people see themselves as hackers and even try to include the views of Raymond in what they see as one wider hacker culture, a view harshly rejected by Raymond himself. Instead of a hacker/cracker dichotomy, they give more emphasis to a spectrum of different categories, such as white hat, grey hat, black hat and script kiddie.
White hat:-
A white hat hacker breaks security for non-malicious reasons, perhaps to test their own security system or while working for a security company which makes security software. The term "white hat" in Internet slang refers to an ethical hacker. This classification also includes individuals who perform penetration tests and vulnerability assessments within a contractual agreement. The EC-Council , also known as the International Council of Electronic Commerce Consultants has developed certifications, course ware, classes, and online training covering the diverse arena of Ethical Hacking.
Black hat:-
A "black hat" hacker is a hacker who "violates computer security for little reason beyond maliciousness or for personal gain" (Moore, 2005). Black hat hackers form the stereotypical, illegal hacking groups often portrayed in popular culture, and are "the epitome of all that the public fears in a computer criminal". Black hat hackers break into secure networks to destroy data or make the network unusable for those who are authorized to use the network.
Part 1: Targeting
The hacker determines what network to break into during this phase. The target may be of particular interest to the hacker, either politically or personally, or it may be picked at random. Next, they will port scan a network to determine if it is vulnerable to attacks, which is just testing all ports on a host machine for a response. Open ports—those that do respond—will allow a hacker to access the system.
Part 2: Research and Information Gathering
It is in this stage that the hacker will visit or contact the target in some way in hopes of finding out vital information that will help them access the system. The main way that hackers get desired results from this stage is from "social engineering", which will be explained below. Aside from social engineering, hackers can also use a technique called "dumpster diving". Dumpster diving is when a hacker will literally search through users' garbage in hopes of finding documents that have been thrown away, which may contain information a hacker can use directly or indirectly, to help them gain access to a network.
Part 3: Finishing The Attack
This is the stage when the hacker will invade the preliminary target that he/she was planning to attack or steal. Many "hackers" will be caught after this point, lured in or grabbed by any data also known as a honeypot (a trap set up by computer security personnel).
Grey hat:-
A grey hat hacker is a combination of a Black Hat and a White Hat Hacker. A Grey Hat Hacker may surf the internet and hack into a computer system for the sole purpose of notifying the administrator that their system has been hacked, for example. Then they may offer to repair their system for a small fee.
Elite hacker:-
A social status among hackers, elite is used to describe the most skilled. Newly discovered exploits will circulate among these hackers. Elite groups such as Masters of Deception conferred a kind of credibility on their members.
Script kiddi:-
A script kiddie (or skiddie) is a non-expert who breaks into computer systems by using pre-packaged automated tools written by others, usually with little understanding of the underlying concept—hence the term script (i.e. a prearranged plan or set of activities) kiddie (i.e. kid, child—an individual lacking knowledge and experience, immature).
Neophyt:-
A neophyte, "n00b", or "newbie" is someone who is new to hacking or phreaking and has almost no knowledge or experience of the workings of technology, and hacking.
Blue hat:-
A blue hat hacker is someone outside computer security consulting firms who is used to bug test a system prior to its launch, looking for exploits so they can be closed. Microsoft also uses the term BlueHat to represent a series of security briefing events.
Hacktivis:-
A hacktivist is a hacker who utilizes technology to announce a social, ideological, religious, or political message. In general, most hacktivism involves website defacement or denial-of-service attacks. Nation state Intelligence agencies and cyberwarfare operatives of nation states.
Attack:-
A typical approach in an attack on Internet-connected system is:
1. Network enumeration: Discovering information about the intended target.
2. Vulnerability analysis: Identifying potential ways of attack.
3. Exploitation: Attempting to compromise the system by employing the vulnerabilities found through the vulnerability analysis.
In order to do so, there are several recurring tools of the trade and techniques used by computer criminals and security experts.
Security exploit:-
A security exploit is a prepared application that takes advantage of a known weakness. Common examples of security exploits are SQL injection, Cross Site Scripting and Cross Site Request Forgery which abuse security holes that may result from substandard programming practice. Other exploits would be able to be used through FTP, HTTP, PHP, SSH, Telnet and some web-pages. These are very common in website/domain hacking.
Techniques
Vulnerability scanner:-
A vulnerability scanner is a tool used to quickly check computers on a network for known weaknesses.Hackers also commonly use port scanners. These check to see which ports on a specified computer are "open" or available to access the computer, and sometimes will detect what program or service is listening on that port, and its version number. (Note that firewalls defend computers from intruders by limiting access to ports/machines both inbound and outbound, but can still be circumvented.)
Password cracking:-
Packet sniffer:-
A packet sniffer is an application that captures data packets, which can be used to capture passwords and other data in transit over the network.
Spoofing attack (Phishing):-
A spoofing attack involves one program, system, or website successfully masquerading as another by falsifying data and thereby being treated as a trusted system by a user or another program. The purpose of this is usually to fool programs, systems, or users into revealing confidential information, such as user names and passwords, to the attacker.
Rootkit:-
A rootkit is designed to conceal the compromise of a computer's security, and can represent any of a set of programs which work to subvert control of an operating system from its legitimate operators. Usually, a rootkit will obscure its installation and attempt to prevent its removal through a subversion of standard system security. Rootkits may include replacements for system binaries so that it becomes impossible for the legitimate user to detect the presence of the intruder on the system by looking at process tables.
Social engineering:-
When a Hacker, typically a black hat, is in the second stage of the targeting process, he or she will typically use some social engineering tactics to get enough information to access the network. A common practice for hackers who use this technique, is to contact the system administrator and play the role of a user who cannot get access to his or her system.
Trojan horses:-
A Trojan horse is a program which seems to be doing one thing, but is actually doing another. A trojan horse can be used to set up a back door in a computer system such that the intruder can gain access later. (The name refers to the horse from the Trojan War, with conceptually similar function of deceiving defenders into bringing an intruder inside.)
Viruses:-
A virus is a self-replicating program that spreads by inserting copies of itself into other executable code or documents. Therefore, a computer virus behaves in a way similar to a biological virus, which spreads by inserting itself into living cells. While some are harmless or mere hoaxes most computer viruses are considered malicious.
Worm:-
Key loggers:-
A key logger is a tool designed to record ('log') every keystroke on an affected machine for later retrieval. Its purpose is usually to allow the user of this tool to gain access to confidential information typed on the affected machine, such as a user's password or other private data. Some key loggers uses virus-, trojan-, and rootkit-like methods to remain active and hidden. However, some key loggers are used in legitimate ways and sometimes to even enhance computer security. As an example, a business might have a key logger on a computer used at a point of sale and data collected by the key logger could be used for catching employee fraud.
Thursday, 1 October 2015
Hack your mobile's password or pattern without loosing data(with and without root)
Method 1 : Flashing zip file from CWM recovery
For this method, it is necessary that your phone has a custom recovery like Clockworkmod (CWM) installed in it.
Downloads :
1. Lock Screen Security Bypass for Android.
Procedure :
1. Download and copy the zip file on your phone external memory. You may use
memory card reader for that.
2. Switch off your device. You need to boot into CWM recovery mode now .Note
that every device requires different key combination to enter recovery mode.
(power button + Vol.+/Vol.-).
3. After landing into CWM recovery , select install zip from sd card option.
4.On the next screen choose zip from sd card option. This will show all the files loacated on the sdcard.
5. Just navigate to the zip file which you have just transferred on your
phone.
6. select the file and confirm the installation by selecting 'Yes-Install
LockScreen_Security_Bypass.zip'.
7.Wait for the flashing process to get completed. It will hardly take few
minutes to complete.
8. After it completes successfully, select 'reboot system now' option from
the recovery mode itself to restart your phone.
9. If you see the pattern/password lock after rebooting, don't worry, just
enter any random pattern or password and your phone will get unloacked.
Method 2: Using Aroma File Manager
This method does not require USB debugging as well as root access.
Downloads:
1. Aroma File Manager for Android.
Procedure:
Step 1: Download and copy the Aroma File manager.zip file to your memory
card. Remember not to extract it.
Step 2: Now switch off your phone completely until it vibrates. Boot the
phone into recovery mode. Different phones have different ways to enter
recovery mode. If you don’t know how to boot into recovery, you can Google it
or you can also ask us in comments below.
In case of CWM recovery:
Step 3: Mount all partitions including sd-ext (if you have it).
Step 4: Navigate to the install zip from sdcard option and select it. On the
next screen selectchoose zip from sdcard option. Then navigate to the Aroma
File Manager zip file which you’ve just transferred on your phone. Confirm
the installation by selecting Yes option.
In case of Stock recovery (Samsung e3):
Step 3: In stock recovery, there is no option to mount partitions, so
navigate to the apply update from sdcard option and select it. Now navigate
to the Aroma File Manager zip file and flash it.
Step 4: In Aroma File Manager, click on menu option and then go to settings
and select Mount All Partitions. Now, exit from Aroma File Manager and re-
flash it. Now, you will see each partition is mounted in it.
Step 5: (For both Stock/ CWM recovery) In Aroma file manager, navigate to the
/data/system folder.
Note: If you have sd-ext mod to increase internal storage, go to /sd-
ext/system/
Step 6: In /data/system/ folder delete the following files if they exist:
gesture.key (for pattern lock)
password.key (for password lock)
locksettings.db
locksettings.db-shm
locksettings.db-wal
signature.key
sparepassword.key
Step 7: After deleting, exit the Aroma file manger and restart your phone.
If the pattern/password lock still exit then don’t panic just try any random
pattern/password and the phone will get unlocked
For this method, it is necessary that your phone has a custom recovery like Clockworkmod (CWM) installed in it.
Downloads :
1. Lock Screen Security Bypass for Android.
Procedure :
1. Download and copy the zip file on your phone external memory. You may use
memory card reader for that.
2. Switch off your device. You need to boot into CWM recovery mode now .Note
that every device requires different key combination to enter recovery mode.
(power button + Vol.+/Vol.-).
3. After landing into CWM recovery , select install zip from sd card option.
4.On the next screen choose zip from sd card option. This will show all the files loacated on the sdcard.
5. Just navigate to the zip file which you have just transferred on your
phone.
6. select the file and confirm the installation by selecting 'Yes-Install
LockScreen_Security_Bypass.zip'.
7.Wait for the flashing process to get completed. It will hardly take few
minutes to complete.
8. After it completes successfully, select 'reboot system now' option from
the recovery mode itself to restart your phone.
9. If you see the pattern/password lock after rebooting, don't worry, just
enter any random pattern or password and your phone will get unloacked.
Method 2: Using Aroma File Manager
This method does not require USB debugging as well as root access.
Downloads:
1. Aroma File Manager for Android.
Procedure:
Step 1: Download and copy the Aroma File manager.zip file to your memory
card. Remember not to extract it.
Step 2: Now switch off your phone completely until it vibrates. Boot the
phone into recovery mode. Different phones have different ways to enter
recovery mode. If you don’t know how to boot into recovery, you can Google it
or you can also ask us in comments below.
In case of CWM recovery:
Step 3: Mount all partitions including sd-ext (if you have it).
Step 4: Navigate to the install zip from sdcard option and select it. On the
next screen selectchoose zip from sdcard option. Then navigate to the Aroma
File Manager zip file which you’ve just transferred on your phone. Confirm
the installation by selecting Yes option.
In case of Stock recovery (Samsung e3):
Step 3: In stock recovery, there is no option to mount partitions, so
navigate to the apply update from sdcard option and select it. Now navigate
to the Aroma File Manager zip file and flash it.
Step 4: In Aroma File Manager, click on menu option and then go to settings
and select Mount All Partitions. Now, exit from Aroma File Manager and re-
flash it. Now, you will see each partition is mounted in it.
Step 5: (For both Stock/ CWM recovery) In Aroma file manager, navigate to the
/data/system folder.
Note: If you have sd-ext mod to increase internal storage, go to /sd-
ext/system/
Step 6: In /data/system/ folder delete the following files if they exist:
gesture.key (for pattern lock)
password.key (for password lock)
locksettings.db
locksettings.db-shm
locksettings.db-wal
signature.key
sparepassword.key
Step 7: After deleting, exit the Aroma file manger and restart your phone.
If the pattern/password lock still exit then don’t panic just try any random
pattern/password and the phone will get unlocked
Tuesday, 29 September 2015
How to find and delete duplicate files on pc
I am always a victim of lots of useless and redundant data in my PC. Out of all these useless files, a good percentage of the content is the duplicate data. It’s always difficult to find duplicate files and delete them manually. So today I am going to show how can you find the duplicate files and delete them from your computer.
There are hundreds of good software out there that can find the duplicate files in your system and remove them. But, I found Duplicate Files Finder light and fast to use. Duplicate Files Finder is a software that locates the duplicate files (same content, but not necessarily same name). You can delete them manually or create links. The search used in this software is very fast compared other programs of the similar nature with hashing algorithms.
Firstly, all the files are sorted by size as duplicate files will have equal size. Other search software use hashing algorithms that scan the files completely. Also, additional caching of files improves the performance.
Take a look at some of its features:
- Comparison is Byte by byte
- Search is very fast
- Support for symbolic links and hardlinks
- Good interface for deleting files and creating links
- Variety search options
How To Find Duplicate Files in your system?
Step 1. First you need to download and install the Duplicate File Finder setup in your system. Download for Windows and Linux from HERE.
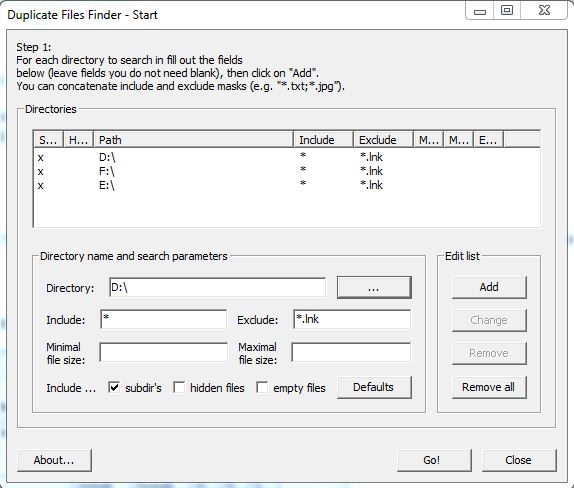
Step 2. Open the Duplicate Files Finder and you will find this app window as shown in image below. Now click the button highlighted in the picture to choose the directory in which you are expecting the duplicate files. Once you selected the directory, click OK.
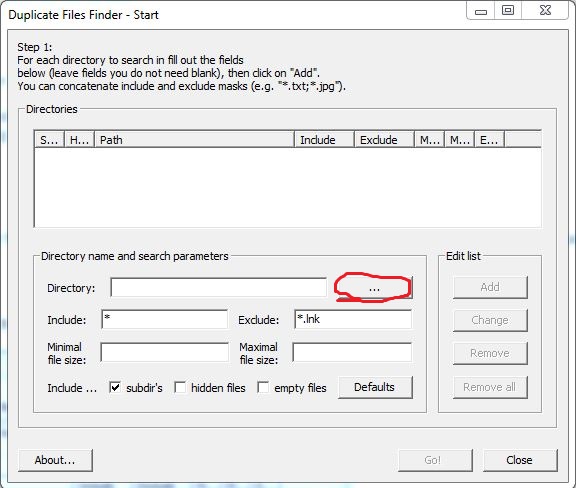
Step 3: Now click on Add which is located at right-hand side of directory option. Duplicate Files Finder gives you option to add multiple directories or folders at once in which you wishing to find the duplicate files.
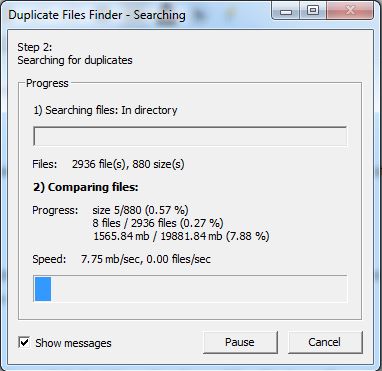
Step 4. Once you selected all the directories or folders, click Go! Your Duplicate Files Finder will perform a quick search and return the names of duplicate files as well as in which folder they are being stored.
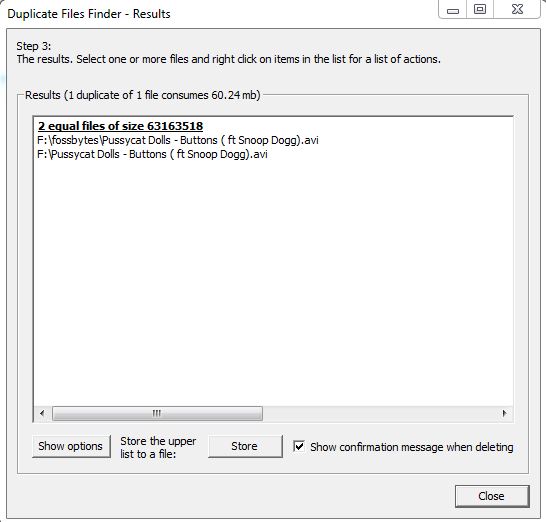
Now You can delete the duplicate files manually. Have fun using the software.
Sunday, 13 September 2015
Catch the guy who is using your fake Facebook account easily and quickly
Is someone using your fake Facebook account and spoiling your name.Then this is the right place for you. Here in this post I will be telling how to catch that guy
Facebook chat runs on XMPP protocol now which is not peer-2-peer, so it is not possible to determine the IP address of the user through Facebook Chat using Netstat command. All i will be doing is use some social engineering skills and default ‘Banner grabbing‘ technique of a web server.
Banner Grabbing is an enumeration technique used to get information about a particular computer system on a network/internet (Information like: Operating system, browser, IP address, etc.)
Steps in finding an IP address of a fake Facebook user:
#1. Collect as much information about the fake profile as you can and identify all of the people who are connected to the profile. Make a list of connected people to this account who are your real life friends.
#2. Select any one of your close friend or relative on that list (select most trusted person). The person which you have selected will be doing all the job for you. If there is nobody you can trust on this list then ask any of your trusted friend to Befriend this fake profile user.
#3. Ask your Friend to start chatting with this fake user casually everyday. (Remember whatever you do should remain between you can your friend. do not let it spread among other close friends)
#4. Now Go tohttp://iptracking.geniushackers.comand fill in your valid email address and enter any name in the ‘Link Name’ field. Click Generate.
[ * ] Geniushackers website is down. Alternatively you can use other tools for tracking IP. You can find the list of Tracking tools here: List of IP tracking tools (Tracing facebook user location).
#5. In the next page you will get a unique link. Just copy this unique link.
#6. Next goto https://goo.gl and paste your ‘Unique URL’ (that is too long) in the text field and clickshorten URL. You will get short URL that will look something like this:http://goo.gl/mC5gFF.
#7. Ask your friend to send this shortened URL to the Fake profile user along with some nice message via chat such that he should click on that URL. Example message:
“Hey wassup? i found this really nice story, read here:http://goo.gl/mC5gFF“
#8 As soon as the fake user clicks on that link, you will receive an email with a link to his System details. example details:
Steps for Tracing fake profile user and catching the culprit:
Now that you have found out the IP address of the fake user, its time to know more about this fake user.
#9. Gotohttp://www.iptrackeronline.com and enter the ‘IP address’ of the fake user, click submit query.
#10. On the new page, scroll down a bit and you will get to see all the details like ISP, Area-code, Postal-code, etc. regarding his IP address along with a Map.
#11. Relate these details with the suspect. If you are not able to suspect anyone then approach your attorney or lawyer, he will file the necessary documents for the ISP to disclose the subscriber details for the IP address.
#12. If you are suspecting anyone but not sure if its him then repeat the steps 3 to 8 for this suspect. You can take help of the same friend and ask him to craft some different message accompanied by IP tracking link for this suspect.
#13. As soon as your suspect clicks this link, you will have his IP address. Now match his IP address with the IP address of the Fake user. If there is a match, well congrats!! you have successfully nabbed the culprit.
This post is posted for one of my friend who was in trouble and asked help from me.Hope is problem is solved.
This post is posted for one of my friend who was in trouble and asked help from me.Hope is problem is solved.
Friday, 11 September 2015
Meet “Steve Jobs of Robotics” – Man Who is Making World’s First Humanoid Smartphone
Tomotaka Takahashi, considered as Steve Jobs of robotics, aims to gift humanity a talking humanoid smartphone very soon. An associate professor at the University of Tokyo, Tomotaka Takahashi has built a lifestyle around his smart gadgets and plans to extend his robot family now.
It is no denying the fact that we are going to be surrounded by Artificial Intelligence soon. Robots engaged in our chores; you might be greeted at the reception by one of those in the near future. But the question is how near is that near future, how soon?
Tomotaka Takahashi, a roboticist and an associate professor at the University of Tokyo plans to do it, well, really soon. He strategies to build a pocket size robot with features of Siri. And he is ready to unveil his hybrid four-limbed Siri. Did you get the plot? It is similar to Tony Stark giving Jarvis a body!! C’mon people.
Takahashi in his own words, he wants to become “Steve Jobs of Robotics”. He aims to build smartphones in the humanoid form, more charismatic and stylish. And he is putting all his work to build world’s first humanoid smartphone.
Japan has been the centre of artificial intelligence and robotics development. Suidobashi Heavy Industries, Japan are one of the biggest names in the Robotics industries with the beast Kuratas as their poster bot. And it won’t be long that yet another brilliant robot design comes from the country. Only, this time it won’t be a fighter bot, but a friendly humanoid smartphone that would give you a nice company.
Contrary to the plot of Artificial Intelligence taming humans famously prophecized by Stephen Hawking, Takahashi believes his smart bot would be your one of the bust buddies and will not kick off any uprising.
Most of our apprehension for the AI should be credited to Terminator series. Robots getting self-awareness is also a major concern among many, but it does not deter Takahashi who plans to build a lovable Astroboy type friendly humanoid smartphone bot.
Takahashi has built several smart machines that are into the Guinness World Records, the longest distance covered by a battery-operated remote-controlled model car, the first companion robot in space, and the highest altitude for a robot to have a conversation.
But, all the research and developments aside, we still don’t know when the robots will become ubiquitous. Tomotaka Takahashi gives hope with his humanoid smartphone idea, however, there would be many concerns even if the robots suddenly start becoming available in the markets.
For all the robots, first, the manufacturers have to assure the public that their bots are safe and won’t go Terminator on them.
Second, the cost of these advanced machines would affect their density in the public domain.
Third, it would be a headache for law enforcement agencies. The fact that the case of drones with guns mounted is still controversial, robots arriving into the scene would only increase the chaos.
Tech companies and enthusiasts are giving their best efforts to create safe and cost effective robots, so now we can say without doubt that we will soon have robots in our society, but the important question should be, is humanity ready for them?
Having anything to add to this article about the man who wants to become Steve Jobs of Robotics? Tell us in comments below.
It is no denying the fact that we are going to be surrounded by Artificial Intelligence soon. Robots engaged in our chores; you might be greeted at the reception by one of those in the near future. But the question is how near is that near future, how soon?
Tomotaka Takahashi, a roboticist and an associate professor at the University of Tokyo plans to do it, well, really soon. He strategies to build a pocket size robot with features of Siri. And he is ready to unveil his hybrid four-limbed Siri. Did you get the plot? It is similar to Tony Stark giving Jarvis a body!! C’mon people.
Takahashi in his own words, he wants to become “Steve Jobs of Robotics”. He aims to build smartphones in the humanoid form, more charismatic and stylish. And he is putting all his work to build world’s first humanoid smartphone.
Japan has been the centre of artificial intelligence and robotics development. Suidobashi Heavy Industries, Japan are one of the biggest names in the Robotics industries with the beast Kuratas as their poster bot. And it won’t be long that yet another brilliant robot design comes from the country. Only, this time it won’t be a fighter bot, but a friendly humanoid smartphone that would give you a nice company.
Contrary to the plot of Artificial Intelligence taming humans famously prophecized by Stephen Hawking, Takahashi believes his smart bot would be your one of the bust buddies and will not kick off any uprising.
Most of our apprehension for the AI should be credited to Terminator series. Robots getting self-awareness is also a major concern among many, but it does not deter Takahashi who plans to build a lovable Astroboy type friendly humanoid smartphone bot.
Takahashi has built several smart machines that are into the Guinness World Records, the longest distance covered by a battery-operated remote-controlled model car, the first companion robot in space, and the highest altitude for a robot to have a conversation.
But, all the research and developments aside, we still don’t know when the robots will become ubiquitous. Tomotaka Takahashi gives hope with his humanoid smartphone idea, however, there would be many concerns even if the robots suddenly start becoming available in the markets.
For all the robots, first, the manufacturers have to assure the public that their bots are safe and won’t go Terminator on them.
Second, the cost of these advanced machines would affect their density in the public domain.
Third, it would be a headache for law enforcement agencies. The fact that the case of drones with guns mounted is still controversial, robots arriving into the scene would only increase the chaos.
Tech companies and enthusiasts are giving their best efforts to create safe and cost effective robots, so now we can say without doubt that we will soon have robots in our society, but the important question should be, is humanity ready for them?
Having anything to add to this article about the man who wants to become Steve Jobs of Robotics? Tell us in comments below.
Hacking Someone's Facebook Password Using Some Software Or Website? No Sir You Can't!
Hacking Someone's Facebook Password Using Some Software Or Website? No Sir You Can't!

Do you know there are over thousands of websites and software that claim to hack Facebook password of any account? They'd ask you the victim's profile ID, maybe your credentials and some money too and will reportedly tell you the password which, to be honest, never works. Ever wonder why? Let me tell you why, they're FAKE! They're a scam which tricks you somehow in losing your money or your own Facebook account. Just give it a thought, why would Zuckerberg and his team spend Billions of Dollars on Facebook if one could hack it in less than a minute? Today, we'll take a look at this topic in detail with some example websites and software and get answers to some common related questions.
Back in 2005, I came across a mechanism that reportedly hacked Yahoo mail password for a user using some simple tricks. It didn't work for me for obvious reasons but I didn't stop believing the possibility until I grew up to realize how helpless I am here. One of the major concerns of large organizations like Facebook and Yahoo is security because of the super sensitive information about people they have. Several hundred million dollars are spend yearly by these organizations to ensure security and then there's these websites that claim to undo all that protection in less than a minute.
The Facebook password cracking Websites and Software
Let's start with some examples here. I googled the subject and picked the top results without order. Didn't care to search harder because there are thousands such and I know that all are FAKE.
So let's look at this GETFBHACK.com.

Their FREE Facebook hacker program is said to be capable of cracking the password of any Facebook user within a day. Sounds cool, I could try it out, but my Norton Antivirus rejected the file straight away.
I also picked up another one. This Hack-Fbook-Password asks me to enter the profile ID of a user and it will crack the password. I said Okay and began the process.

It ran certain algorithms to determine the password and finally landed me on a page that said I could DOWNLOAD the password IF I fill an online survey first. Those of you who've been redirected to surveys would know they don't work and are put just so to get traffic and earn money.
I said maybe I should leave the website now but hey, they gave me a prize!

So I just became the luckiest person in my city just like that!
Now tell me, how can a sane person believe in all this?
The truth!
Let me get this straight to you, these websites do nothing at all just waste your time and are never able to do the job. In fact, downloaded programs just make the situation worse when you run them. I had my Norton Antivirus to guard me otherwise I could be in severe danger currently.
These software are mostly keyloggers and tracking programs that record your keystrokes and action and steal personal information from your computer in the background and send it to their master servers. So ultimately a hacker wannabe gets hacked, how ironic!
From now on in the post, I'll be using the word 'Hacker' for these websites and software since you're no more in the position to be called that.
Why do these 'Hackers' do all that?

Setting up websites, maintaining them and developing software is not an easy task. It requires some money. So why do these 'hackers' do all the hassle? It's because they get equivalent or more money in return. They can extract your credit card details and other banking info from your system and use it for their advantage. They can hack your account and use it for wrong purposes. Give me one reason why one wouldn't steal money and hack accounts for no loss.
Why people fall in their webs?

Why do people try to use such unreal hacking procedures? It's because it's unreal to me, it's unreal to you but not to those who are not much familiar with the working of a software. They get in the web of these hackers and eventually get screwed up pretty bad without consent.
The websites give guarantees and also portray their 'imaginary' happy customers so as to trick a reader. Such tactics are simple but really powerful and serves to their advantage in most cases. This is also why there are thousands of such websites available.
So is Facebook account an 'unbreakable fortress'?

Well, NO. Facebook accounts can be hacked. No online service is foolproof and that is because of the flaws and bugs in their software. There are several ACTUAL hackers in the world who can analyse a website's security and use that against it thus making hacking a reality.
But I'm 100% sure none of them uses these scam and fake websites that claim to do the impossible. You can check out our hacking section to know more.
I'll end the 'lesson' with an idiom, "look before you leap". Focus, think and then follow. In case of any queries or confusions head over to the comments section. Cheers :)
Saturday, 5 September 2015
Linux 101 Hacks eBook Free Download
- “Linux 101 Hacks” by Ramesh Natarajan is available in PDF format for free. This book gives you practical examples to build a strong foundation in Linux.Table of Contents:-
- Chapter 1: Powerful CD Command Hacks
- Hack 1. Use CDPATH to define the base directory for cd command
- Hack 2. Use cd alias to navigate up the directory effectively
- Hack 3. Perform mkdir and cd using a single command
- Hack 4. Use “cd -” to toggle between the last two directories
- Hack 5. Use dirs, pushd and popd to manipulate directory stack
- Hack 6. Use “shopt -s cdspell” to automatically correct mistyped directory names on cd
- Chapter 2: Date Manipulation
- Hack 7. Set System Date and Time
- Hack 8. Set Hardware Date and Time
- Hack 9. Display Current Date and Time in a Specific Format
- Hack 10. Display Past Date and Time
- Hack 11. Display Future Date and Time
- Chapter 3: SSH Client Commands
- Hack 12. Identify SSH Client Version
- Hack 13. Login to Remote Host using SSH
- Hack 14. Debug SSH Client Session
- Hack 15. Toggle SSH Session using SSH Escape Character
- Hack 16. SSH Session Statistics using SSH Escape Character
- Chapter 4: Essential Linux Commands
- Hack 17. Grep Command
- Hack 18. Find Command
- Hack 19. Suppress Standard Output and Error Message
- Hack 20. Join Command
- Hack 21. Change the Case
- Hack 22. Xargs Command
- Hack 23. Sort Command
- Hack 24. Uniq Command
- Hack 25. Cut Command
- Hack 26. Stat Command
- Hack 27. Diff Command
- Hack 28. Display total connect time of users
- Chapter 5: PS1, PS2, PS3, PS4 and PROMPT_COMMAND
- Hack 29. PS1 – Default Interaction Prompt
- Hack 30. PS2 – Continuation Interactive Prompt
- Hack 31. PS3 – Prompt used by “select” inside shell script
- Hack 32. PS4 – Used by “set -x” to prefix tracing output
- Hack 33. PROMPT_COMMAND
- Chapter 6: Colorful and Functional Shell Prompt Using PS1
- Hack 34. Display username, hostname and current working directory in the prompt
- Hack 35. Display current time in the prompt
- Hack 36. Display output of any command in the prompt
- Hack 37. Change foreground color of the prompt
- Hack 38. Change background color of the prompt
- Hack 39. Display multiple colors in the prompt
- Hack 40. Change the prompt color using tput
- Hack 41. Create your own prompt using the available codes for PS1 variable
- Hack 42. Use bash shell function inside PS1 variable
- Hack 43. Use shell script inside PS1 variable
- Chapter 7: Archive and Compression
- Hack 44. Zip command basics
- Hack 45. Advanced compression using zip command
- Hack 46. Password Protection of Zip files
- Hack 47. Validate a zip archive
- Hack 48. Tar Command Basics
- Hack 49. Combine gzip, bzip2 with tar
- Chapter 8: Command Line History
- Hack 50. Display TIMESTAMP in history using HISTTIMEFORMAT
- Hack 51. Search the history using Control+R
- Hack 52. Repeat previous command quickly using 4 different methods
- Hack 53. Execute a specific command from history
- Hack 54. Execute previous command that starts with a specific word
- Hack 55. Control the total number of lines in the history using HISTSIZE
- Hack 56. Change the history file name using HISTFILE
- Hack 57. Eliminate the continuous repeated entry from history using HISTCONTROL
- Hack 58. Erase duplicates across the whole history using HISTCONTROL
- Hack 59. Force history not to remember a particular command using HISTCONTROL
- Hack 60. Clear all the previous history using option -c
- Hack 61. Substitute words from history commands
- Hack 62. Substitute a specific argument for a specific command
- Hack 63. Disable the usage of history using HISTSIZE
- Hack 64. Ignore specific commands from the history using HISTIGNORE
- Chapter 9: System Administration Tasks
- Hack 65. Partition using fdisk
- Hack 66. Format a partition using mke2fsk
- Hack 67. Mount the partition
- Hack 68. Fine tune the partition using tune2fs
- Hack 69. Create a swap file system.
- Hack 70. Create a new user
- Hack 71. Create a new group and assign to an user
- Hack 72. Setup SSH passwordless login in OpenSSH
- Hack 73. Use ssh-copy-id along with ssh-agent
- Hack 74. Crontab
- Hack 75. Safe Reboot Of Linux Using Magic SysRq Key
- Chapter 10: Apachectl and Httpd Examples
- Hack 76. Pass different httpd.conf filename to apachectl
- Hack 77. Use a temporary DocumentRoot without modifying httpd.conf
- Hack 78. Increase the Log Level temporarily
- Hack 79. Display the modules inside Apache
- Hack 80. Show all accepted directives inside httpd.conf
- Hack 81. Validate the httpd.conf after making changes
- Hack 82. Display the httpd build parameters
- Hack 83. Load a specific module only on demand
- Chapter 11: Bash Scripting
- Hack 84. Execution Sequence of .bash_* files
- Hack 85. How to generate random number in bash shell
- Hack 86. Debug a shell script
- Hack 87. Quoting
- Hack 88. Read data file fields inside a shell script
- Chapter 12: System Monitoring and Performance
- Hack 89. Free command
- Hack 90. Top Command
- Hack 91. Ps Command
- Hack 92. Df Command
- Hack 93. Kill Command
- Hack 94. Du Command
- Hack 95. lsof commands.
- Hack 96. Sar Command
- Hack 97. vmstat Command
- Hack 98. Netstat Command
- Hack 99. Sysctl Command
- Hack 100. Nice Command
- Hack 101. Renice Command
Author(s): Ramesh Natarajan
File Size: 838 KB
File Format: PDF
Number of pages: – 140
Download Link: – Linux 101 Hacks
File Size: 838 KB
File Format: PDF
Number of pages: – 140
Download Link: – Linux 101 Hacks
Friday, 4 September 2015
Faster WiFi Technology Boosts WiFi Speed Up to Ten Times
Tired of your slow WiFi speed and all those tips to increase the Wifi signal strength? Here’s a new that will cheer you up. Researchers at Oregon State University have unveiled a newly invented technology that can enhance the WiFi speed and bandwidth by 10 times. This revolutionary tech uses LED lights to transmit the information.
This 10 times faster WiFi technology could be integrated with the pre-existing WiFi systems and it will lead to the reduction in bandwidth issues in crowded places and homes with multiple users. This has been made possible due to the recent advancements in the LED technology that makes LED light modulation easy and thus opening the option of using light for wireless transmission.
Thinh Nguyen, an OSU associate professor, who worked with Alan Wang said: “In addition to improving the experience for users, the two big advantages of this system are that it uses inexpensive components, and it integrates with existing WiFi systems.”
How this 10 times faster WiFi technology works?
The first prototype WiFo – uses LEDs that emit an invisible cone of light (beyond human visible spectrum) of one-meter square area, where data can be received. To overcome this small usage area, researchers have created a hybrid system that switches between the existing WiFi system and multiple LED transmitters on the ceiling.
Nguyen said: “I believe the WiFO system could be easily transformed into a marketable product, and we are currently looking for a company that is interested in further developing and licensing the technology.”
What are the speed improvements?
This new system can transmit 100 megabits/second. The current WiFi systems have same bandwidth, but it gets divided in multiple devices. Here, the new hybrid system provides 50-100 megabits to all users.
What are the advantages?
This 10 times faster WiFi technology can cure the bandwidth problems in crowded places where bandwidth gets divided. In homes, if there are multiple devices and they are connected to same WiFi connection, this new technology would eradicate the speed problems.
The receivers of the data are tiny photodiode and they cost less than a dollar. They could be easily integrated with the current systems (WiFi routers, laptops, smartphones, tablets and more) using a USB port. (With inputs fromoregonstate.edu)
Are you eagerly waiting for this technology? Tell us in comments.
Free App from Microsoft to Move Your Files from Windows 7 to Windows 10
Free App from Microsoft to Move Your Files from Windows 7 to Windows 10
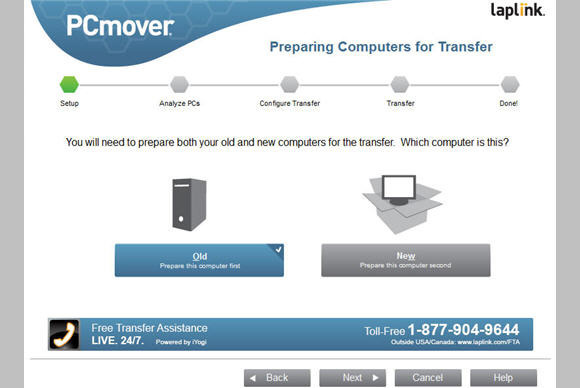
Microsoft partners with Laplink Software, Inc. to provide free download of Laplink’s file transfer software PCmover.
This tool is used to transfer files and folders from one computer to another, this will be free version until August 2016 and is for personal, non-commercial use only.
You can download your copy on Microsoft official page. Install the software on your new and old PCs to transfer your files, folders and settings, this won’t affect the files or personalized settings when you transfer your data.
If you want to use PCmover Express, then your old and new PCs must be connected to the Internet.
According to Thomas Kool, Laplink’s CEO “We’re fully committed to this relationship with Microsoft in support of all Windows users, Our latest version of PCmover makes it easier than ever for customers running Windows XP, all the way to the latest release of Windows 10, to migrate their personal files, folders, and other settings to their new PC.”
Note: Apps install on your old PC need to be manually re-installed on your new PC
Subscribe to:
Posts (Atom)